checkpoint firewall scaled
A checkpoint firewall is a type of firewall that monitors traffic as it travels through the network, and blocks or allows traffic based on predefined rules. This helps to mitigate security threats by preventing unauthorized access to network resources and stopping malicious activity before it can occur. It is useful for Enterprise Network too
What is a checkpoint firewall?
A checkpoint firewall is a security measure that is used to control access to systems. It works by monitoring traffic and comparing it to predetermined criteria. If the traffic matches the criterion, then the traffic is allowed to pass.
Checkpoint firewall benefits:
Checkpoint firewall benefits include:
- Reducing the attack surface: A checkpoint firewall limits the number of areas that a hacker can attack from, reducing the potential damage they can cause.
- Securing critical systems: A checkpoint firewall helps protect your systems from malicious attacks that may attempt to exploit vulnerabilities in them.
- Enhancing security posture: By blocking malicious traffic, a checkpoint firewall can help improve your overall security posture.
- Enhancing performance: By restricting which traffic is allowed through the firewall, checkpoint firewalls can often improve network performance.
- Maintaining compliance with regulations: By limiting access to certain ports and protocols, a checkpoint firewall can help maintain compliance with applicable regulations.
What are the different types of checkpoint firewalls?
There are many types of checkpoint firewalls, each with its own unique benefits and drawbacks. Here’s a look at the three most popular types:
Application-level checkpoint firewall:
This type of firewall filters traffic based on the application(s) being used. For example, a school might use an application-level checkpoint firewall to limit students’ access to certain websites during lunchtime.
Network-layer checkpoint firewall:
These firewalls filter traffic based on the network layer (IP address, port number, etc.). For example, a company might use a network-layer checkpoint firewall to block employees from accessing unauthorized websites or sending malicious emails from their work accounts.
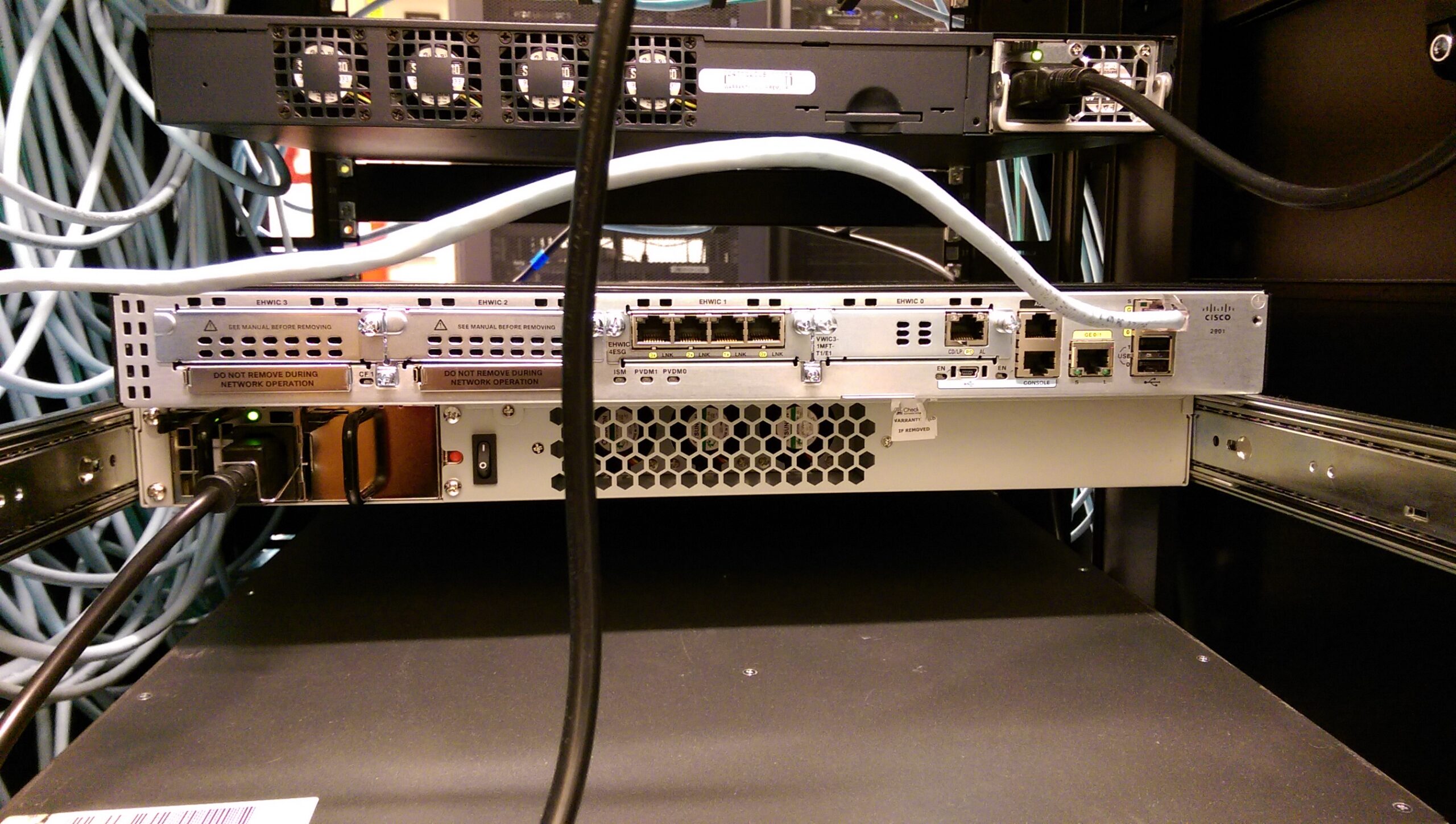
Security appliance checkpoint firewall:
This type of firewall is usually installed on the internal network and monitors traffic for threats such as viruses and malware.
How do checkpoint firewalls work?
When a computer is first connected to the network or when it starts up, special software on the computer looks for a “known good” copy of the operating system. If the computer finds no such copy, it requests one from a server known as a “checkpoint.”
A checkpoint firewall is a special kind of firewall that uses checkpoints to help protect computers and networks from malicious activity. When you connect to the Internet, your computer sends out packets asking other computers whether they have a copy of the latest version of Windows. If not, your computer will request and download this latest version from a server known as a “checkpoint.”
A checkpoint firewall helps protect your computer by storing recent versions of Windows on its hard drive. When you start up your computer, it checks with the checkpoint to see if there is an update waiting for it.
Checkpoint firewall deployment scenarios:
Deployment scenarios for checkpoint firewalls are broad and varied. They include both standalone and distributed deployments, as well as in-line or embedded deployments. Inline deployments are typically used in networks that have a limited number of firewall instances, while distributed deployments are more common when a firewall is deployed across multiple sites.
One deployment scenario is to deploy a checkpoint firewall at the edge of the network, between the internal network and the internet. This type of deployment can help protect sensitive data and applications from outside attacks.
Another scenario is to deploy checkpoints inbound and outbound on an individual host or group of hosts. This type of deployment can help enforce security policies on individual systems or groups of systems.
In conclusion, a checkpoint firewall is a valuable tool for protecting your network against malicious attacks. By configuring and using a checkpoint firewall, you can ensure that your network remains safe and protected from malicious activity.